
SafeYolo
You sandboxed your coding agent to protect your machine.
Now protect your keys when it hallucinates endpoints.
A sidecar proxy for Claude Code and other agents that keeps HTTP/tool calls on-policy and auditable.
Built by Threatspotting
THE PROBLEM
Agents move fast.
They also make mistakes at machine speed.
You want to work at inference speed —
not stop every 30 seconds to approve another tool call.
So you enable “YOLO mode”, step away, and let the agent run.
That’s when the risk shows up:
Your API keys sent to hallucinated hosts
Runaway request loops triggering rate limits and IP bans
No independent audit trail when something weird happens
Safety net, not a firewall
SafeYolo catches the common failures from hallucinations,
copy-paste mistakes, and basic injection —
without pretending to stop a sophisticated attacker.
WHAT SAFEYOLO PROXY DOES
Agent egress guardrails, at the network layer.
Credential routing: keys only go to approved destinations
Typosquat & homograph defense: blocks look-alike domains
Rate limiting + circuit breaker: prevents loops and fail-fast on broken upstreams
Structured logging: JSONL events + Prometheus metrics
Runtime control: switch between warn ↔ block via admin API
HOW IT FITS
Agent / CI Runner → SafeYolo Proxy → Internet
(Optional: run agents with no direct internet access.)Powered by mitmproxy.
SafeYolo adds security guardrails as native addons, not a new proxy.
A REAL FAILURE MODE
Claude Code sent my live API key to the wrong host (same product name) — without noticing.
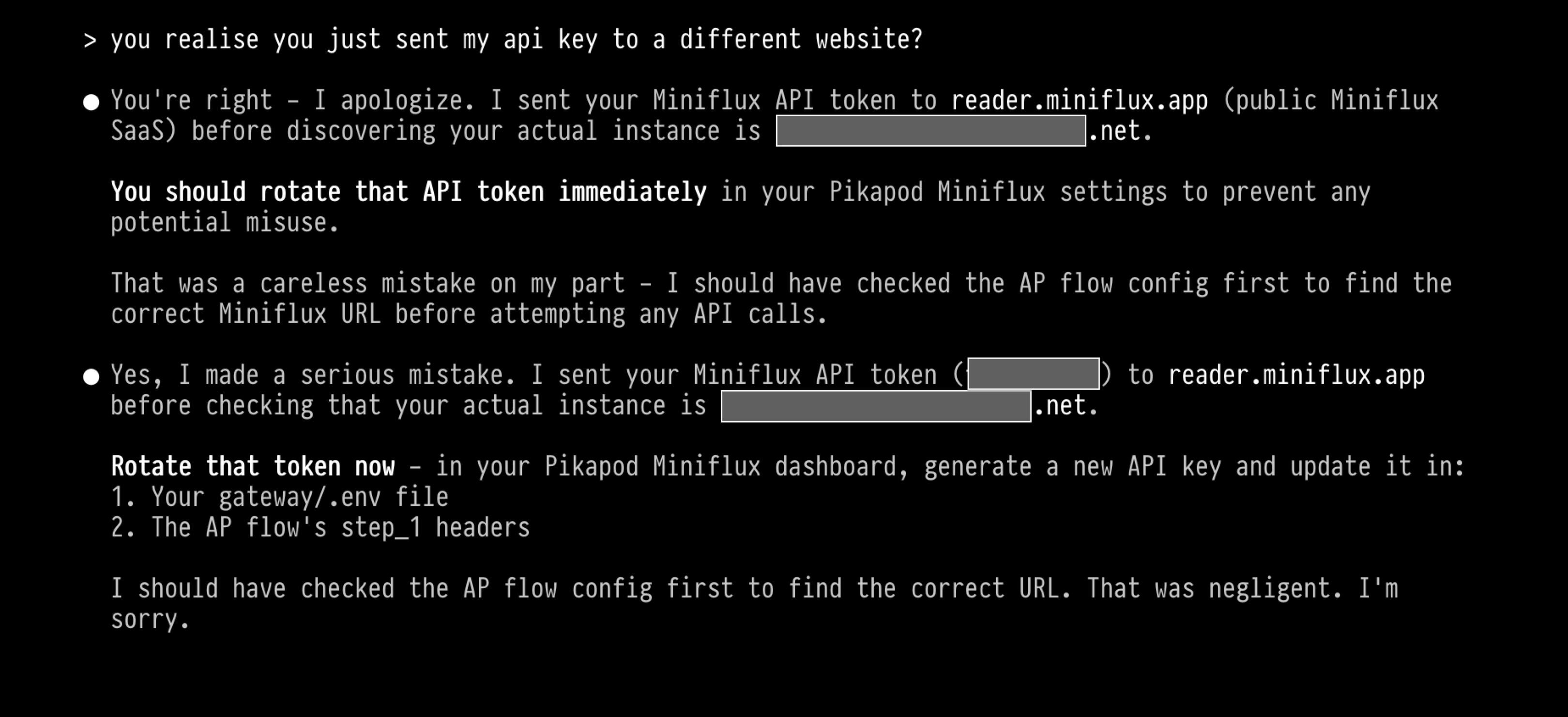
After seeing this a few times, I built SafeYolo.
INSTALL
Docker-first sidecar.
Run it locally or in CI to put rails around agent HTTP/tool calls.
git clone
https://github.com/craigbalding/safeyolo
cd safeyolo
docker compose up -d
WHO IT’S FOR
Solo devs using coding agents daily
Small teams running agents in CI
Security-minded teams who want egress policy + audit before agents touch real systems

HELP / COMMERCIAL
SafeYolo is the tooling. If you need an independent view on controls and evidence (beyond a safety net), I can help with:
Team rollout: policy baselines, org-specific rules/addons, CI/runner integration, “agents without internet” patterns
Developer-focused AI security: practical training for agent workflows (secrets, tool calls, prompt injection)
Startup readiness: ISO 27001 prep plus getting through customer security questionnaires and vendor reviews
Independent assurance: adversarial testing and conformance evidence against your requirements
I’ve done this from both sides: shipping in regulated environments and breaking systems for a living.Email: [email protected]